The Core Pillars of Digital Infrastructure Maintenance
In our interconnected world, digital infrastructure forms the invisible backbone of almost everything we do. From global communication to everyday online tasks, it powers our lives. Experts predict that worldwide IT spending will hit a massive $5.61 trillion in 2025. A large part of this growth comes from efforts to modernize this infrastructure. This huge investment highlights a crucial point: regular, professional maintenance is not just a good idea, it’s absolutely essential. It ensures our digital systems stay strong and keep working without interruption.
This guide will take a deep dive into all sides of digital infrastructure maintenance. We will look at the basic parts that need constant care, explore new predictive methods, and tackle tough issues like security and environmental impact. We will also highlight the need for expert support, including vital Tech repair and data recovery services, to make sure every piece of your digital world works perfectly. Our aim is to give you a clear plan for building and keeping digital foundations that are tough, safe, and ready for tomorrow.
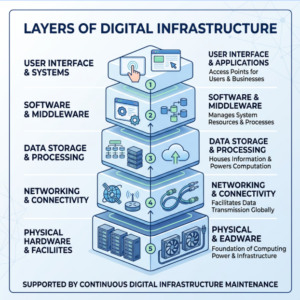

Digital infrastructure is a complex ecosystem, encompassing the physical hardware and software technologies that underpin modern operations. Its resilience hinges on the meticulous maintenance of its core components. These include everything from physical servers, networking equipment, and storage devices to the intricate software, cloud services, and connectivity solutions that bind them together.
At its foundation, digital infrastructure relies on robust hardware components. This includes the physical servers that host applications and data, the fiber optics and cabling that enable high-speed data transmission, and the specialized equipment supporting edge computing and IoT integration. Each piece of hardware has a lifecycle, and without professional hardware auditing and regular checks, components can degrade, leading to performance bottlenecks or catastrophic failures. For instance, a failing hard drive in a server can lead to data loss, while a faulty network switch can bring an entire operation to a halt. When such issues arise, having access to expert tech repair and data recovery services becomes paramount to minimize downtime and preserve critical information. These specialized services understand the nuances of various hardware systems and can diagnose, repair, and recover data efficiently, ensuring business continuity.
Beyond the physical, the network architecture itself demands constant attention. This involves maintaining routers, switches, firewalls, and wireless access points to ensure seamless connectivity and secure data flow. Cloud services, whether public, private, or hybrid, also fall under the maintenance umbrella, requiring regular configuration reviews, performance tuning, and security updates to optimize their efficiency and cost-effectiveness. Data storage systems, from on-premise arrays to distributed cloud storage, need consistent monitoring for integrity, capacity, and accessibility.
The integration of IoT devices and edge computing further complicates the maintenance landscape. These distributed components require specialized protocols for monitoring, updating, and securing. Ensuring their optimal performance and security across vast geographical areas or numerous devices demands a scalable approach to maintenance. Effective digital infrastructure maintenance is about understanding the component lifecycle, predicting potential failures, and having the expertise to intervene before minor issues escalate into major disruptions. It’s a continuous process that ensures the infrastructure can meet current demands while adapting to future scalability requirements.
Proactive vs. Predictive Digital Infrastructure Maintenance
The evolution of maintenance strategies in digital infrastructure has moved significantly beyond simply reacting to failures. We now distinguish between reactive, proactive, and predictive approaches, each offering distinct advantages.
Reactive maintenance is the most basic approach, where actions are taken only after a system or component has failed. This is often akin to waiting for a car to break down completely before taking it to the mechanic. While seemingly cost-effective in the short term by avoiding upfront maintenance expenses, it invariably leads to unplanned downtime, emergency repairs, higher overall costs due to expedited services, and potential data loss or security breaches. For critical digital infrastructure, a purely reactive approach is unsustainable and highly risky.
Proactive maintenance, on the other hand, involves scheduled maintenance activities performed at regular intervals, regardless of the component’s current condition. This includes routine software updates, hardware inspections, and system optimizations. Think of it like regular oil changes for your car – you perform them based on mileage or time, aiming to prevent issues. This approach significantly reduces the likelihood of unexpected failures and extends the lifespan of assets. However, it can sometimes lead to unnecessary maintenance if components are still performing optimally, or it might miss issues that develop rapidly between scheduled checks.
Predictive maintenance represents the cutting edge of infrastructure care. This advanced approach leverages real-time data, often collected through IoT sensors embedded within hardware and software, combined with predictive analytics and machine learning algorithms. These technologies analyze patterns, identify anomalies, and forecast potential failures before they occur. For example, sensors might detect subtle changes in a server’s temperature, fan speed, or power consumption that indicate an impending hardware failure. With this insight, maintenance can be scheduled precisely when needed, optimizing resource allocation and minimizing disruption. Predictive maintenance maximizes system uptime, extends asset lifespan, and achieves significant cost efficiencies by preventing costly emergency repairs and avoiding unnecessary scheduled maintenance. It relies heavily on professional diagnostic tools and sophisticated data analysis capabilities to translate raw data into actionable insights.
Maintenance Model Description Key Characteristics Advantages Disadvantages Reactive Fixes issues after they occur. Unplanned downtime, emergency repairs. Minimal upfront planning. High downtime, high repair costs, unpredictable. Proactive Scheduled maintenance at fixed intervals. Regular checks, updates, replacements. Reduces unexpected failures, extends asset life. Can be inefficient (doing maintenance too early), may miss sudden issues. Predictive Uses data to forecast failures before they occur. IoT sensors, AI/ML, real-time monitoring, analytics. Maximizes uptime, optimizes resources, cost-efficient, extends asset life. Requires significant initial investment in technology and expertise. The Role of Patching in Digital Infrastructure Maintenance
Patch management is a critical, yet often underestimated, component of maintaining secure and resilient digital infrastructure. It involves the systematic process of identifying, prioritizing, acquiring, installing, and verifying software and firmware updates across an organization’s entire digital ecosystem. The National Institute of Standards and Technology (NIST) Special Publication 800-40, for instance, provides comprehensive guidance on developing an enterprise patch management strategy, emphasizing its role as a form of preventive maintenance.
In today’s threat landscape, patching is more vital than ever. Cyber threats are constantly evolving, and vulnerabilities in software or firmware can be quickly exploited by malicious actors, leading to data breaches, operational disruptions, and severe reputational damage. Regular security patches address these vulnerabilities, closing potential backdoors and strengthening the infrastructure’s defenses. This process extends beyond operating systems to include applications, network devices, cloud services, and even IoT devices.
An effective patch management strategy requires professional deployment and adherence to compliance standards. This means not only applying patches promptly but also testing them thoroughly to ensure compatibility and prevent unintended side effects. Firmware updates for hardware components are equally important, as they can enhance performance, add new features, and, crucially, address security flaws at a deeper level. Without consistent firmware updates, hardware can become a weak link in the security chain.
Beyond security, patching also plays a role in maintaining functionality and performance. Software versioning ensures that all components are running optimally, benefiting from bug fixes and performance enhancements. This continuous improvement contributes to overall system stability and efficiency.
The importance of proactive maintenance extends beyond core infrastructure components to broader organizational responsibilities, including user experience and legal compliance. For instance, ensuring that digital platforms are accessible to all users, including those with disabilities, is not just a best practice but often a legal requirement. Just as we maintain the technical integrity of our systems, we must also maintain their usability and inclusivity. Services specializing in Digital accessibility maintenance help organizations ensure their digital presence meets standards like WCAG, mitigating legal risks and enhancing user experience. This holistic view of maintenance, encompassing both technical resilience and user-centric design, is essential for truly robust digital infrastructure.
Security Hardening and Operational Visibility
In the intricate world of digital infrastructure, security hardening and comprehensive operational visibility are non-negotiable. With cyber spending expected to grow 15% in 2025 to reach $212 billion globally, security must be embedded throughout the infrastructure design, not treated as an afterthought.
A core tenet of building resilient infrastructure is attack surface reduction. This involves systematically disabling unused features and services by default, requiring explicit enablement only for those functionalities that are essential. This approach significantly narrows the potential entry points for attackers. Hardening guides provide detailed recommendations and best practices for implementing these security changes, ensuring that devices and systems are configured to protect sensitive data and withstand attacks.
Implementing a zero-trust networking model is another critical step. This framework operates on the principle of “never trust, always verify,” meaning no user or device is inherently trusted, regardless of their location within or outside the network perimeter. Every access request is authenticated, authorized, and continuously validated. This is often achieved through strong network segmentation, using VLANs, firewalls, and DMZs to isolate different parts of the network and control traffic flow.
For managing sensitive infrastructure, out-of-band management is crucial. This involves creating a physically separate network dedicated solely to managing devices, distinct from the operational data network. This separation prevents attackers who might compromise the main network from gaining control over critical infrastructure components. Access to this management network should be highly restricted, often limited to dedicated administrative workstations.
User authentication is a major vulnerability point. Implementing phishing-resistant Multi-Factor Authentication (MFA) for all accounts accessing systems is a fundamental safeguard. Technologies like FIDO2-compliant security keys offer a stronger defense against phishing attacks than traditional MFA methods.
Beyond prevention, operational visibility is key to detecting and responding to threats swiftly. This requires comprehensive monitoring, logging, and telemetry data collection. Centralized logging aggregates logs from all devices and applications into a single platform, making it easier to analyze security events. A Security Information and Event Management (SIEM) system further enhances this by correlating events, detecting patterns indicative of attacks, and generating alerts.
Effective configuration management is also vital. Configurations should be stored centrally and pushed to devices, rather than allowing devices to be the sole source of truth. Any unauthorized configuration changes must trigger immediate alerts, enabling rapid detection and remediation of tampering. Regular security auditing, including penetration testing and vulnerability scanning, helps identify weaknesses before attackers do. By combining robust hardening techniques with comprehensive visibility, organizations can build a digital infrastructure that is both secure and resilient against sophisticated threats.
Sustainability and Energy Planning for Modern Systems
The rapid expansion of digital infrastructure, particularly data centers, presents significant challenges and opportunities in energy management and sustainability. Data centers, the physical backbone of our digital world, are voracious consumers of electricity. Currently, data centers consume approximately 4.4% of total U.S. electricity, and this demand is projected to soar. According to IEA reports, global electricity demand from data centers could more than double by 2030. This exponential growth is largely driven by the increasing adoption of AI workloads, which are far more power-intensive than traditional computing. AI-focused data centers, for instance, may require 30-50 kW per rack, a substantial increase compared to the 5-10 kW per rack typical for conventional setups.
This escalating power demand necessitates a strategic approach to energy management and power planning. Organizations building and maintaining digital infrastructure must prioritize energy efficiency and integrate sustainable practices. This includes optimizing cooling systems, which are often the second-largest energy consumer in a data center after the IT equipment itself. Advanced cooling technologies, such as liquid cooling and artificial intelligence-driven climate control, can significantly reduce energy waste.
Strategic energy partnerships are becoming crucial. Collaborating with energy providers who understand the unique requirements of modern digital infrastructure can help secure reliable, clean power sources. This includes exploring options for renewable integration, such as direct power purchase agreements from solar or wind farms. The goal is not just to reduce the carbon footprint but also to ensure a stable and cost-effective power supply in regions where grids are already strained by increasing demand.
Sustainable growth in digital infrastructure requires careful planning that balances rapid expansion with environmental responsibility. This involves selecting geographically advantageous locations for data centers with access to abundant renewable energy and cooler climates, which can naturally reduce cooling loads. It also means designing infrastructure with modularity and scalability in mind, allowing for efficient upgrades and expansions without necessitating entirely new builds.
Professional facility management plays a pivotal role in implementing these strategies. From ensuring optimal power distribution units (PDUs) to managing uninterruptible power supplies (UPS) and backup generators, every aspect of power infrastructure needs meticulous maintenance and monitoring. The focus is on creating resilient power systems that can not only handle the projected 165% growth in global data center power demand by 2030 but also do so in an environmentally conscious manner. By embracing energy-efficient designs, renewable energy sources, and smart power management, we can build a digital infrastructure that is both high-performing and sustainable for the future.
Developing a Strategic Roadmap for Infrastructure Longevity
Building and maintaining digital infrastructure for the long haul requires more than just reactive fixes; it demands a well-defined strategic roadmap. This roadmap serves as a blueprint for ensuring the infrastructure remains robust, scalable, secure, and aligned with evolving business objectives.
The first step in developing such a roadmap is a comprehensive assessment of the existing infrastructure. This involves evaluating current hardware, software, network architecture, cloud deployments, and security posture. Organizations often discover over-provisioned cloud resources or legacy systems that are no longer efficient, highlighting areas for optimization.
Next, it’s crucial to define clear business objectives. What are the organization’s growth targets? What new technologies or services are planned? The infrastructure roadmap must directly support these goals, ensuring that technology serves business strategy, not the other way around. Based on these objectives, architecture standards should be established, promoting consistency, interoperability, and security across all systems.
Scalability planning is paramount. Digital infrastructure must be designed to grow and adapt without requiring complete overhauls. This means anticipating future demands, such as the increasing adoption of AI and edge computing. The 5G edge computing market, for instance, is predicted to grow by 49.8% from 2023 to 2030, necessitating infrastructure that can support distributed computing resources closer to end-users.
Budgeting for digital infrastructure is a significant consideration. While infrastructure budgets typically account for 15-25% of an organization’s total IT budget, this figure can surge to 40-60% for AI-intensive projects due to their higher power and compute requirements. The roadmap should include a detailed financial plan, balancing capital expenditure (CapEx) for new hardware and software with operational expenditure (OpEx) for ongoing maintenance, cloud services, and staffing.
A realistic implementation timeline with clear milestones and risk mitigation strategies is also essential. This includes planning for phased migration of legacy systems to maintain business continuity and addressing potential challenges like skills gaps or vendor lock-in. Professional consultancy can be invaluable here, offering expert guidance in navigating complex migrations and optimizing resource allocation.
The roadmap must also account for emerging trends. Beyond AI integration and 5G edge computing, organizations are increasingly moving towards cloud-native architectures and hybrid/multi-cloud environments. This requires vendor-neutral strategies and robust governance models to avoid fragmentation and ensure seamless operation. Continuous monitoring of technological advancements and industry best practices is key to keeping the roadmap relevant and future-proof. By proactively planning and adapting, organizations can ensure their digital infrastructure remains a strategic asset, capable of supporting innovation and sustained growth.
Frequently Asked Questions about Digital Infrastructure
What is the difference between digital infrastructure and traditional IT?
Digital infrastructure is a broader concept that encompasses the entire ecosystem required to support modern digital operations. While traditional IT infrastructure primarily focuses on computing, networking, and storage within an organization’s immediate purview, digital infrastructure extends to include critical elements like energy systems, cooling solutions, and physical facilities, especially for high-demand workloads like AI and edge computing. It also considers broader connectivity, sustainability, and resilience across diverse environments, from on-premises data centers to vast cloud deployments and distributed edge networks.
How long does it take to develop a comprehensive maintenance plan?
The timeline for developing a comprehensive digital infrastructure maintenance plan can vary significantly based on the complexity and scale of the environment. Typically, a thorough assessment and design phase requires anywhere from 3 to 6 months. This period allows for a deep dive into existing systems, identification of vulnerabilities, definition of business-aligned objectives, and the creation of detailed maintenance schedules and protocols. More complex systems, or those undergoing significant modernization, may require longer. Engaging professional services for this process can streamline it, leveraging their specialized diagnostic tools and experience to accelerate planning while ensuring accuracy and completeness.
Why is professional maintenance preferred over in-house DIY attempts?
While in-house teams possess valuable institutional knowledge, professional maintenance services offer specialized expertise, advanced diagnostic tools, and guaranteed Service Level Agreements (SLAs) that are often challenging for internal teams to match. Professionals bring a broader perspective on industry best practices, emerging threats, and compliance requirements. They can provide 24/7 monitoring, rapid response capabilities, and access to a wider range of technical skills for complex hardware repairs, software issues, and data recovery. This specialized support ensures higher uptime, enhanced security, and adherence to regulatory standards, ultimately allowing internal teams to focus on strategic initiatives rather than day-to-day troubleshooting.
Conclusion
The journey through digital infrastructure maintenance reveals a landscape of increasing complexity and critical importance. From the foundational hardware and intricate network architectures to the strategic imperative of security hardening and the pressing demands of sustainability, every facet requires meticulous attention. We’ve seen how moving from reactive to predictive maintenance strategies, bolstered by AI and IoT, transforms operational efficiency and resilience. We’ve also underscored the non-negotiable role of patching and comprehensive visibility in safeguarding against ever-evolving cyber threats.
Building and maintaining a future-ready digital infrastructure is about more than just technology; it’s about strategic investment, operational excellence, and a commitment to long-term sustainability. It demands a proactive approach, a security-by-design mindset, and a clear roadmap guided by business objectives and emerging trends. By embracing professional partnerships and expert implementation, organizations can ensure their digital foundations are not just resilient but also agile, secure, and capable of propelling them into the future with confidence.

